Six Costly Data Protection Gaps In Microsoft 365 And How To Close Them
Default Deployments of Microsoft 365 are a Data Loss Disaster Waiting to Happen
If your business relies on Microsoft 365, you can expect reliable access to its applications with very high uptime. But many IT professionals are laboring under a dangerous misconception: that Microsoft provides fully-fledged data protection and long-term data retention for Microsoft 365. The reality is that the emails, attachments, and shared files stored in Microsoft 365 are not protected from the most common and serious data loss issues, ranging
from simple accidental deletions to sophisticated malware attacks.
Thus for many organisations, Microsoft 365 represents a major data protection gap, an unhappy surprise waiting to happen. Too late, they may learn that Microsoft provides only limited features to help restore lost, destroyed or damaged Microsoft 365 data, with nowhere near the backup functionality or robustness with which most businesses protect their other critical applications.

Six Weak Spots in Protection of Microsoft 365 Data
Microsoft has invested heavily in its data centers’ hardware, software, networks, security and operations to ensure high levels of performance, access and uptime for Microsoft 365.
Microsoft 365 can quickly detect and recover from many of its own operational errors, site outages, hardware failures and network issues to meet its service-level agreements, which center on application uptime. But these measures do not protect your business from many common Microsoft 365 data loss issues, e.g., the need to restore an email that got deleted by accident, or a OneDrive for Business file that was misplaced, or a library of SharePoint Online content that became corrupted by a malware attack.
Microsoft offers limited restore capabilities for most Microsoft 365 data, and only retains files for a short time (varying from a few weeks to a few months, depending on the application and contract). You may determine that the data residing in a former employee’s repository or a long-idle project is suddenly important again, only to find that Microsoft did not retain a copy that you can quickly find and recover.
Microsoft 365 Administrators Need to Address Microsoft’s Data Protection Shortcomings in Six Key Areas
1) Accidental Deletion Issues
DATA RISK: In the course of their daily work, IT administrators and ordinary employees routinely delete Microsoft 365 user profiles, Exchange Online emails, attachments & files, OneDrive for Business files, Teams, and SharePoint Online content. These deletions may be accidental in nature, or intentional but later regretted – most of us have suddenly needed to refer to an email that we deleted only yesterday.
SHORTCOMING: These kind of everyday resource deletions are routinely replicated across the network. The age of the resource exacerbates the problem: older data may be hard-deleted and unrecoverable. More recent deletions of newer resources are slightly less problematic, as soft-deleted files and emails may be recoverable in the short term from the Recycle Bin or Recoverable Items folder.
2) Retention Policy Issues
DATA RISK: Changing or misaligned priorities in Microsoft 365 data retention policies can result in data being hard-deleted. This can only be partially mitigated by regular review and updating of retention policies.
SHORTCOMING: Microsoft 365 customers have the onus of managing retention policies, but if for whatever reason a hard-deletion occurs due to aging out of the existing retention policy, Microsoft has no ability to recover the deleted resource.
3) Insider Security Threats
DATA RISK: In addition to routine, non-malicious deletions, Microsoft 365 resources need to be protected against malicious alteration or destruction of data by disgruntled or terminated employees, contractors or partners.
SHORTCOMING: With the exception of relatively recent deletions of relatively new resources, Microsoft does not protect against malicious insider destruction or alteration of Microsoft 365 data.
4) External Security Threats
DATA RISK: Microsoft 365 data is vulnerable to destruction or alteration by a variety of malware threats, most notably ransomware, which encrypts user data and holds it hostage until an online ransom is paid. These attacks may be mounted by hackers, cybercriminals or hostile state actors
SHORTCOMING: By default Microsoft 365 offers limited protections against malware attacks like ransomware, and limited ability to restore malware-encrypted or -altered files to their pre-attack state.
5) Migration from premises-based Microsoft Office
DATA RISK: The migration from the traditional premises-based Microsoft Office application suite to cloud-based Microsoft 365 services usually involves transitioning from a legacy data protection solution to a new cloud-capable one. The two backup solutions are often incompatible, making it impossible to restore legacy data into the new environment.
SHORTCOMING: Microsoft offers no solution to address data loss issues during Office to Microsoft 365 migration. Few third-party data protection solutions integrate backup functionality for Office and Microsoft 365: they usually do one or the other but not both.
6) Legal and Compliance Issues
DATA RISK: Compliance requirements (like the Australian Privacy Principles) and legal issues can exacerbate the business costs of the unprotected data losses described above. Unrecoverable Microsoft 365 data loss can expose the business to government or industry-specific regulatory fines, legal penalties (e.g., damages or lost lawsuits stemming from failure to meet e-discovery or evidentiary requirements), revenue and stock price losses, loss of customer trust, and damage to the company brand.
SHORTCOMING: With all of the associated data loss risks described above, Microsoft can do little to protect organizations using Microsoft 365 against a variety of compliance and legal exposures. For example, after a ransomware attack, a business storing its EU-based customers’ personal data in SharePoint Online might be unable to honor requests for copies of that data, thereby violating GDPR requirements.
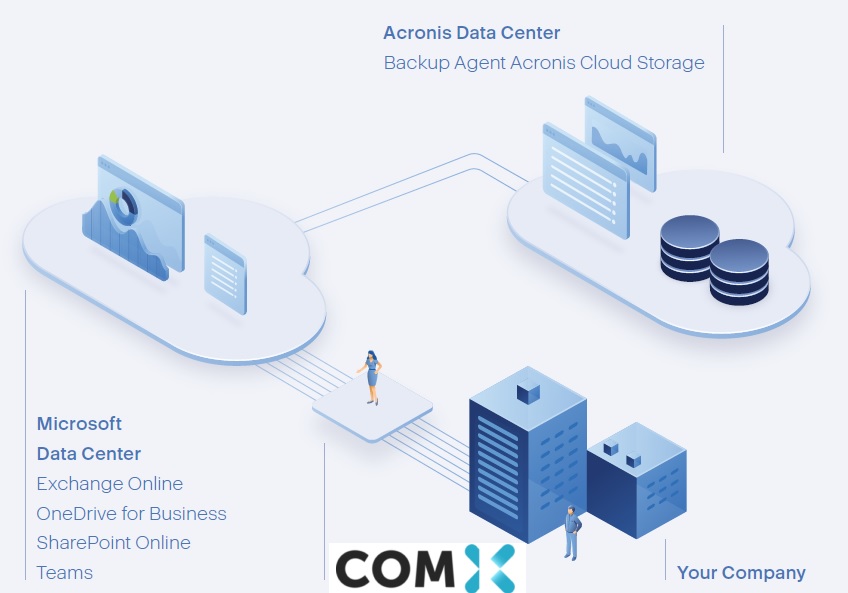
The Bottom Line with Com-X
At Com-X we understand the various soft spots in the default protection of Microsoft 365 data, and we use data protection solutions that address those gaps. We all know the stakes are high: failure to defend an Microsoft 365 data loss can be a big problem. We work with our partner Acronis to Deliver a Complete, Granular Backup For Microsoft 365 with Enhanced Search Features

Exchange Online
Protect emails, attachments, contacts, tasks, group mailboxes, archive mailboxes, and calendars
OneDrive For Business
Safeguard files and folders including all access permissions, if necessary.
SharePoint Online
Secure site collections, team sites, communication sites, and all access permissions settings.
Microsoft Teams
Protect Microsoft Teams data, including team’s name, member list, team channels and their content, team mailbox, meetings, and team sites.
Acronis Cyber Protect Cloud for Microsoft 365 helps Com-X and our customers protect Microsoft 365 data in many ways, including:
A simple and Intuitive user-interface
Administer the solution and perform backup tasks using a user-friendly, modern interface. Reduce costs and time spent learning the solution and implementing it.
Automatic protection for new Microsoft 365 items
Reduce headaches by streamlining backup management for Microsoft 365. New users, groups, and sites are automatically protected.
Quick backup search
Find a file needed in seconds. Enhanced search for mailboxes allows you to search by email subject, recipient, sender, and date. In addition, you can search with word forms or partial information and can also search Teams, OneDrive for Business and SharePoint Online by site item and file name.
Powerful status monitoring
Achieve higher levels of transparency and security thanks to advanced reporting capabilities and backup-status monitoring, including widgets, notifications, and alerts for critical events.
MFA (Multi-Factor Authentication) support
Add an additional layer of security, like authentication via a trusted device or fingerprint. Without MFA, your client’s password is the only verification method.
Multi-level encryption
Safeguard your clients’ data with additional security. At-source, enterprise-grade AES-256 encryption protects backups with irreversibly encrypted passwords.